by Josiah Bussing | May 13, 2025 | Analytics, Productivity, Security, Website Optimization
If your car doesn’t undergo regular maintenance services, it might break down at the most inopportune time and you’ll pay for an expensive repair job. The same scenario can happen to your website if it doesn’t undergo regular inspection. The difference is that a car...
by Josiah Bussing | Nov 28, 2023 | Blog, Security, Website Optimization
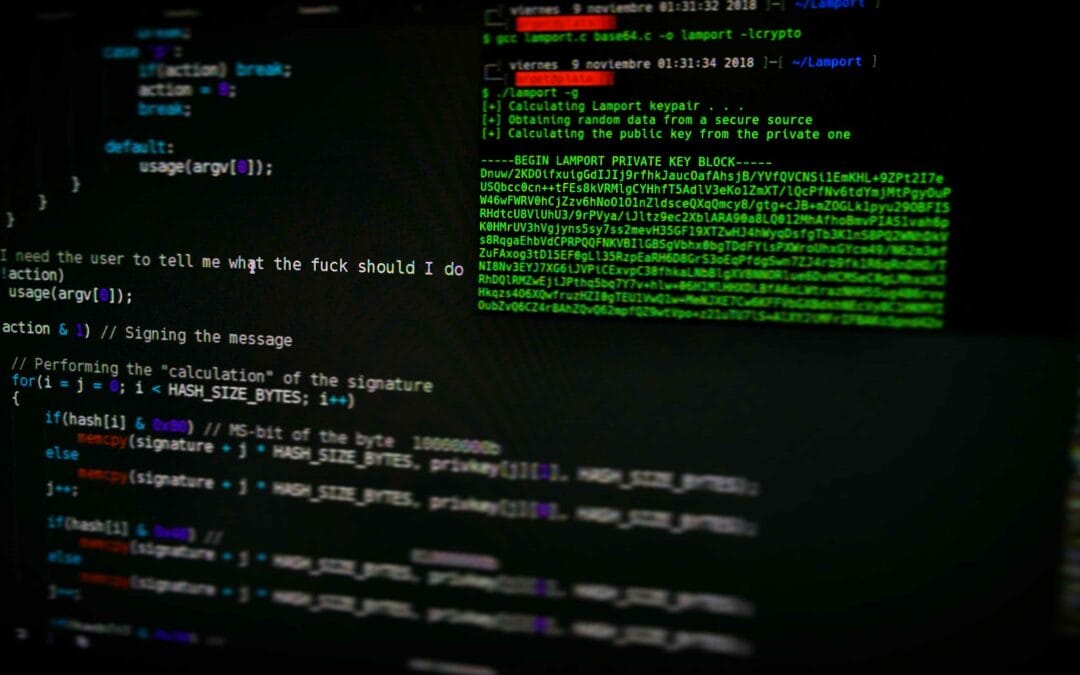
As you’re reading this article, hackers could be attacking your website. Likewise, hackers could attempt to infiltrate your social media platforms and other websites where you’re maintaining accounts with personal information. You could be transacting with your...

by Josiah Bussing | Sep 26, 2023 | Blog, Security
One reason why WordPress has remained the number one website design platform and Content Management System (CMS) is that its plugins and systems are regularly updated with the latest and most advanced security programs. On the flip side, WordPress websites are the...

by Josiah Bussing | Sep 5, 2023 | Blog, Security
Online scammers have their sights trained on you. As you’re reading this article, they could already be infiltrating platforms where you maintain a presence – your business website, email addresses, social media accounts, and third-party e-commerce sites that...

by Josiah Bussing | Apr 25, 2023 | Business, Security, Uncategorized
Paying bills, managing bank accounts, accessing subscriptions, checking social media status, shopping for groceries… all of these daily activities and more are coursed through member-only websites that require passwords. It’s hard enough for you to remember birthdays,...

by Josiah Bussing | Apr 4, 2023 | Security
Are you thinking of setting up a website for your business? Don’t sit on the idea. Once you’ve thought of the domain name for your website, take the necessary steps to have it registered and reserved as soon as possible. If you don’t, you might find yourself a victim...